Deep Engineering #35: Scott Millett on closing the “story gap”
SCQA, the Pyramid Principle, and the decision-forcing close
Building MCP Servers in Production (Live workshop)
Move MCP from demos to production. In this 5-hour online workshop you’ll cover OAuth 2.1 auth pitfalls, OpenTelemetry observability, scaling persistent connections, and managing context growth/cost. Led by Saxo Bank Principal Dev Peder Holdgaard Pedersen. When: Mar 29, 10:30am–3:30pm ET / 7:30am–12:30pm PT.
✍️From the editor’s desk,
Welcome to the 35th issue of Deep Engineering!
This is the second installment in Deep Engineering’s ongoing series adapted from chapter 2 of The IT Strategy Playbook by Scott Millett (Packt; publishing May 2026). Millett is a long-time IT leader and architect who has served in CIO/CTO roles and led large-scale transformation work across multiple sectors (as you saw in Part 1’s “100 Day Plan” boardroom story).
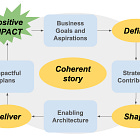
Today’s adaptation focuses on a practical problem: how technical realities become executive decisions. Millett lays out a repeatable approach for communicating strategy—clarifying the single objective, framing the narrative with SCQA (Situation–Complication–Question–Answer), and supporting the recommendation using the Pyramid Principle—so boards and executives can evaluate trade-offs and commit to a direction.
This is well aligned with what US technology leaders are navigating this week: Gartner’s Feb 17 Q&A piece argues that fragmented AI regulation is accelerating spend on AI governance platforms as organizations try to manage compliance and operational risk. At the same time, a multi-industry coalition urged the Commerce Department to preserve the core of the NIST AI Risk Management Framework, a signal that many enterprises are already using it as a shared language for oversight and internal controls. And CISA’s Feb 13 announcement of CIRCIA rulemaking town halls reinforces that incident reporting expectations—and the need to communicate risk and response clearly—remain active, moving targets.
Let’s get started.
Safely Refactor Large Production Codebases with AI
Safely refactor large production codebases with AI. Learn a workflow that pairs Claude Code with ast-grep’s AST-based rewrites for structural guarantees—migrations, guardrails, and best-practice enforcement. Ticket includes Mastering ast-grep + prompt templates. Mar 14, 10–11:30am ET / 7–8:30am PT.
🧠Expert Insight:
The IT Strategy Playbook (Part 2): Closing the Story Gap by Scott Millett
“The most powerful person in the world is the storyteller.” — Steve Jobs
In the early 2000s, Nokia dominated mobile phones. Its strategy, built on exceptional hardware engineering and global supply-chain execution, worked flawlessly until 2007. The company didn’t fall because its engineers lacked insight. It fell because the organization couldn’t convert critical technical knowledge into strategic intent. The signals were present; the translation mechanisms were not.
Nokia’s software teams had long recognized that Symbian’s architecture was reaching its limits. It was fragmented, costly to evolve, and increasingly misaligned with the emerging touch-driven experience. Alternative platforms such as Maemo and later MeeGo were being explored, and the technical risks were well understood within engineering. But these concerns were filtered through a hardware-first culture that interpreted platform limitations as minor technical defects, not as threats to the business model. The communication path from “this architecture will constrain what the business can do” to “this requires a strategic shift” simply wasn’t there.
At the same time, senior leadership continued to optimize short-term device metrics. They still viewed the competitive landscape as a handset battle rather than an ecosystem battle, and the implications of Apple’s and Google’s platform strategies never translated into a unified architectural or strategic response. Nokia’s organizational structure created a communication gradient: technical truths lost meaning as they travelled upward, and strategic signals failed to reorient investment, priorities, or direction.
Within five years, the world’s leading mobile manufacturer was forced to exit the handset business, not because it lacked capability, but because it lacked the ability to translate insight into coherent action. This chapter focuses on the story gap: how to communicate strategic needs clearly, how to ensure signals travel across the organization intact, and how to avoid the silent failures that undermine strategy long before the market ever does.
In this chapter, you’ll learn how to:
Communicate strategic intent with clarity, ensuring technical insight translates into decisions rather than confusion
Structure a coherent strategic narrative using proven frameworks to move from context to conclusion
Develop presentation material that supports decision-making, not just information sharing
Deliver your message effectively, guiding senior stakeholders from understanding to commitment
You will use these skills to close the story gap: translating strategy, architectural intent, and plans into a narrative that enables decisions. Not more slides, but a clear line from context to conclusion, so leaders understand the trade-offs, commit to a direction, and act.
How to Be An Effective Communicator
Delivering a technology strategy is not simply an act of presenting information; it is an act of leadership and influence. The best strategy in the world will fail if the communicator lacks clarity of purpose or the ability to authentically connect with the audience.
Clarify your objective
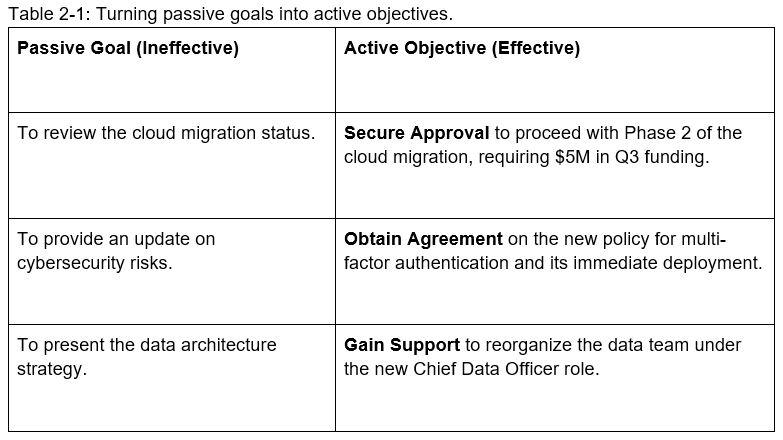
Before you open a slide deck or write a single email, you must answer one question with absolute, non-negotiable clarity: What is the one thing I need the audience to believe or do when I stop speaking or reading? This is the foundation of strategic communication. Without a single, clearly defined objective, your message will lack focus, and your audience will leave confused about the desired next step. Your objective should never be passive, such as “to inform the Board” or “to update the team.” It must be an action verb tied to a measurable outcome. Consider the examples in table 2-1 where we take a passive goal and turn it into an active objective.
When you define your objective down to the ‘one thing,’ you achieve two crucial results:
Elimination of Noise: Every slide, chart, and word you use must directly serve that single objective. If a piece of data doesn’t help you achieve the objective, it belongs in the appendix, or nowhere at all.
Forcing the Answer: By knowing the desired action, you structure your entire presentation to lead logically and inevitably to that conclusion. Your presentation becomes a persuasive roadmap, not a rambling document review.
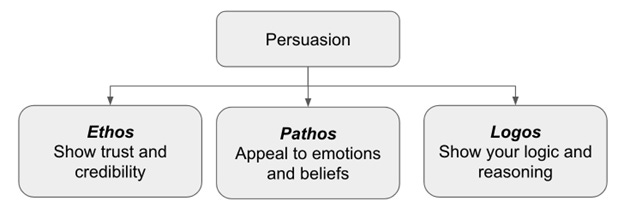
Master the three modes of Persuasion
As an IT leader, you must consciously deploy all three modes to secure buy-in. Relying solely on data (Logos) is rarely enough; you must also establish your credibility (Ethos) and connect your strategy to the organization’s goals and fears (Pathos). The following subsections detail how to weave each of these essential appeals into your strategic narrative to maximize influence and drive action.
The IT Strategy Playbook (Part 2): Closing the Story Gap
This article is Part 2 of Deep Engineering’s ongoing series adapted from The IT Strategy Playbook: How CIOs and CTOs can drive business growth through focused action, architecture, and execution (Packt; publishing May 2026). Each installment is a web-ready adaptation of a draft chapter. I’m refining the manuscript as we go—leave feedback in the comments.
🔍In case you missed it…
🛠️Tool of the Week
Mermaid (mermaid-js/mermaid) is a text-based diagramming tool that turns Markdown-like syntax into diagrams you can embed in docs, RFCs, and strategy decks—useful when you want visuals that stay versionable and easy to review.
📎Tech Briefs
CIRCIA town halls / reporting requirements (US critical infrastructure CIRCIA rulemaking: DHS/CISA scheduled sector-specific virtual town halls (plus two general sessions) to gather additional stakeholder input on refining the scope and burden of the proposed cyber incident reporting rule.
GitHub Agentic Workflows (technical preview): GitHub introduced Markdown-authored “agentic” automations that compile into standard Actions workflows, aiming to make repo automation more natural-language and security-constrained by default.
Attack-surface and app-sec bundling: Cloudflare and Mastercard announced a partnership to combine attack surface monitoring/risk scoring with Cloudflare’s application security controls for faster remediation across internet-facing assets.
CISA KEV update: CISA added four vulnerabilities to its Known Exploited Vulnerabilities Catalog (evidence of active exploitation), reinforcing KEV-driven prioritization for vulnerability management.
VictoriaMetrics LTS release: VictoriaMetrics shipped LTS release v1.122.15 (released 2026-02-13) with bugfixes intended for production observability deployments.
That’s all for today. Thank you for reading this issue of Deep Engineering.
We’ll be back next week with more expert-led content.
Stay awesome,
Divya Anne Selvaraj
Editor-in-Chief, Deep Engineering
If your company is interested in reaching an audience of developers, software engineers, and tech decision makers, you may want to advertise with us.